Educational technology giant Instructure is facing significant scrutiny after threat actor group ShinyHunters claimed responsibility for a large-scale breach involving the company’s widely used Canvas learning management system (LMS). The incident reportedly impacted thousands of schools and universities globally, exposing sensitive student and faculty information and disrupting academic operations during final exam periods.
The breach highlights a growing reality facing SaaS providers and educational institutions alike: modern cyberattacks are increasingly targeting centralized cloud platforms that aggregate enormous amounts of sensitive data.
What Happened?
According to Instructure’s official incident updates, the company initially identified unauthorized activity tied to Canvas in late April 2026. Investigations later revealed that attackers gained access to certain user data, including:
- Names
- Email addresses
- Student ID numbers
- Messages exchanged within Canvas
Instructure stated there was no evidence that passwords, financial information, Social Security numbers, or government identifiers were exposed.
The threat actor group ShinyHunters later claimed responsibility for the attack and alleged they had stolen terabytes of data affecting nearly 9,000 schools and hundreds of millions of users worldwide.
Compounding the situation, attackers reportedly defaced portions of Canvas login infrastructure with extortion messages demanding payment before publicly leaking the data.
The “Second Attack” Escalation
One of the more concerning developments was follow-on activity after initial containment efforts began.
On May 7, reports indicated attackers regained access to portions of the environment and modified public-facing pages, forcing Instructure to temporarily place Canvas into maintenance mode while additional remediation and forensic investigation occurred.
This operational disruption quickly impacted schools and universities relying on Canvas for coursework, communication, and exams. Some institutions reportedly removed access to the platform entirely while evaluating the security risks associated with continued use.
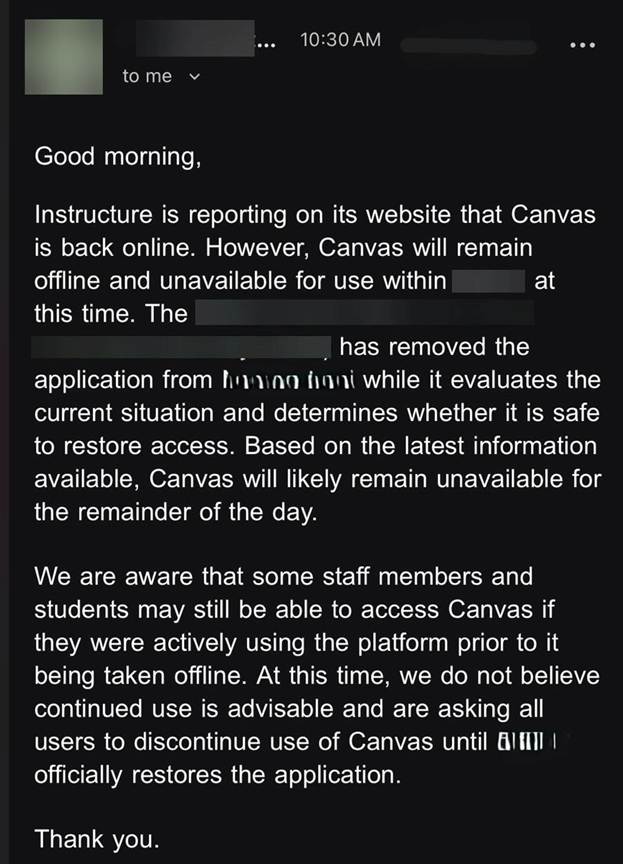
Example institutional alert sent to users during the Canvas outage and security response efforts.
This reinforces an important security lesson: containment does not always equal eradication. Threat actors frequently maintain persistence mechanisms that allow re-entry after organizations believe the incident has been resolved.
Free-for-Teacher Accounts and SaaS Exposure
Several reports tied the compromise to vulnerabilities or weaknesses associated with Canvas “Free-for-Teacher” accounts. Instructure later shut down the program while continuing remediation efforts.
This aspect of the breach is especially important for organizations evaluating SaaS risk. In many environments, lower-tier, legacy, trial, sandbox, or “free” platforms often receive:
- Reduced monitoring
- Less restrictive access controls
- Different authentication standards
- Limited security governance oversight
Threat actors routinely target these overlooked attack surfaces because they can provide an easier path into broader production ecosystems.
Why Educational Institutions Are Increasingly Targeted
The education sector has become an increasingly attractive target for cybercriminals because institutions maintain large volumes of sensitive data while often operating under constrained cybersecurity budgets.
Learning management systems like Canvas centralize:
- Student records
- Faculty communications
- Coursework
- Internal messaging
- Institutional workflows
- Third-party integrations
A compromise of a single SaaS provider can therefore create downstream exposure across thousands of organizations simultaneously.
Additionally, academic institutions frequently experience:
- Decentralized IT administration
- Large user populations
- High turnover rates
- Extensive third-party integrations
- Bring-your-own-device (BYOD) environments
These operational realities create substantial complexity for identity management, access control, monitoring, and incident response.
The Ransom Payment Controversy
Multiple reports indicate Instructure ultimately reached an “agreement” with the attackers to prevent further release of stolen data. Some reporting suggests the company paid a ransom in exchange for assurances that data would be deleted and customers would not face additional extortion attempts.
While organizations facing extortion scenarios must make difficult operational and legal decisions, these incidents reinforce a broader cybersecurity challenge: Even when systems are restored, reputational damage, regulatory scrutiny, operational disruption, and long-term phishing risks can persist long after an incident concludes.
Key Security Takeaways for Organizations
The Instructure incident highlights several important lessons for organizations relying on SaaS platforms and third-party cloud providers.
1. SaaS Platforms Still Require Security Testing
Organizations should regularly assess:
- Authentication and access controls
- API exposure
- Third-party integrations
- Logging and monitoring coverage
Penetration testing and cloud security assessments can help identify weaknesses before attackers do.
2. Legacy or “Free” Services Can Introduce Risk
Attackers commonly target:
- Test or sandbox environments
- Legacy accounts
- Trial services
- Unused integrations
Security governance should extend beyond primary production systems.
3. Containment Does Not Always Mean Eradication
Threat actors often maintain persistence after initial remediation. Organizations should validate:
- Session and token revocation
- Credential rotation
- Third-party access exposure
- Potential lateral movement paths
4. Monitoring and Detection Are Critical
Organizations should maintain visibility into:
- Identity and authentication activity
- SaaS administrative logs
- Privileged access changes
- Suspicious external access attempts
Managed SIEM, threat monitoring and cybersecurity incident response services can significantly improve detection and response timelines during active incidents.
Final Thoughts
The Canvas breach shows how a compromise involving a single cloud platform can rapidly escalate into a global operational and reputational crisis. For educational institutions, SaaS providers, and enterprises alike, the incident serves as another reminder that cybersecurity resilience now depends heavily on cloud governance, third-party risk management, and rapid incident response maturity.
As threat actors continue targeting centralized platforms with large user populations, organizations should proactively evaluate their own SaaS security posture before attackers identify weaknesses first.
Official updates can be found via Instructure’s incident update page.


